Last updated on December 18th, 2025 at 07:29 am
On-chain malware means harmful code is stored or referenced on a public blockchain instead of on a normal web server. Hackers can hide instructions or data inside smart contracts, and one technique that has been observed is called EtherHiding. Attackers place small pieces of malicious code, or payloads, on blockchains like Ethereum or the BNB Smart Chain, and then have normal-looking web pages or downloads fetch that code. This lets the harmful program reach a victim without the attacker hosting the malware on their own servers.
State actors have used this trick in recent campaigns, and security researchers found that a group tracked as UNC5342, which is linked to North Korea, used EtherHiding to hide a JavaScript loader named JADESNOW inside a web page. That loader reads code from a smart contract, then runs a backdoor called INVISIBLEFERRET. Because smart contract data is public and cannot be removed, this makes the malware very hard to take down once it is placed on-chain.

The attackers do not always send a normal program file to the victim; instead, they use social tricks like fake job offers or coding tests that ask a developer to run a sample. When the sample runs, it silently contacts the blockchain and pulls the actual malicious code. The blockchain call often uses a read-only method, so it does not leave a normal transaction trail, increasing stealth and making traditional detection tools less effective.
Implications for DeFi Security and Auditing
DeFi and other blockchain projects rely on smart contracts and on their immutability to build trust. That same immutability and openness can be used against defenders. If attackers store malware or control information on-chain, they gain a persistently available command channel that is hard to censor or remove. This raises new concerns about cyberwarfare, as nation-states can exploit blockchain vulnerabilities to mount long-lived operations that are resistant to takedown.
Smart contract security teams and auditors have historically focused on bugs in the code that runs on-chain, but now they must also consider off-chain behaviour that is controlled from the chain. A contract might look safe in a static audit but still be used as a storage point for harmful payloads. Auditors will need to expand their checks to include patterns in data stored in contracts and the ways contracts are referenced by external scripts. This change affects how DeFi projects think about threat models and how they design their monitoring systems.
The use of on-chain malware by groups tied to North Korea shows that blockchain-based attacks can be part of state-level strategies. These attacks aim not only to steal cryptocurrency but also to gather credentials, spy on systems, and create resilience against standard law enforcement and takedown methods. For defenders, this means that blockchain vulnerabilities must be treated as a national and industry security issue.
RELATED: Blockchain Security: The Importance of Smart Contracts Audits
Potential Defence frameworks for protocols
A stronger approach to smart contract security is needed, with one important step being runtime monitoring of contract storage and calls. Security teams can build tools to watch for unusual patterns in smart contract data, like encoded payloads or frequent updates to storage that do not match the contract intent. This class of monitoring helps reveal when a contract is being used as a hidden content store. Research projects that add dynamic analysis and runtime shields to smart contracts show that this is possible and useful.
Another defence is to harden developer environments and reduce risky behaviours, and companies should treat unsolicited coding tests and downloads as high risk. Websites used for hiring should be checked, and developers should run unknown samples only in isolated sandbox machines. Using dedicated full nodes for blockchain queries instead of public RPC endpoints can also improve visibility and allow teams to filter or log suspicious read-only calls.
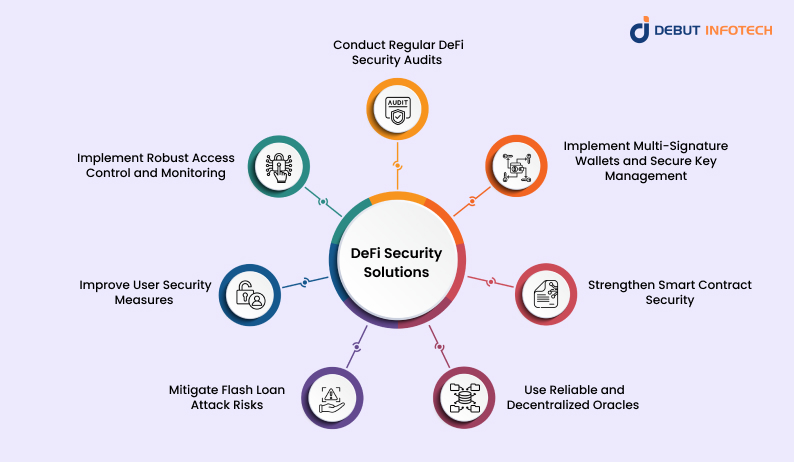
Improvements in smart contract security tooling are also needed. New detection systems that look for malicious intent in bytecode or in on-chain storage could alert teams sooner. Machine learning and opcode-level analysis can find strange control flows and odd data patterns that human reviewers might miss. Sharing threat intelligence on suspicious contract addresses and known EtherHiding infrastructure among firms will accelerate detection and response across the industry.
In Conclusion,
On-chain malware is a new and serious problem with state actors, including groups linked to North Korea, adopting techniques like EtherHiding to embed malware into smart contracts and to use the blockchain as a resilient delivery channel. This shift shows how threat groups are learning to take advantage of the very traits that make blockchain useful, such as permanence, decentralisation and open access. It also shows how cyberwarfare is moving into environments that were once thought to be too transparent for covert operations. By hiding malicious code within contract storage or by making off-chain scripts pull instructions directly from on-chain data, attackers can create command channels that are almost impossible to shut down and extremely hard to trace.
This raises the stakes for smart contract security and makes cyberwarfare more complex, as defenders must now consider risks beyond traditional vulnerabilities, such as reentrancy or access-control bugs. Instead, they face a new class of threats that use the blockchain as infrastructure rather than as a target. To keep up, defenders must update how they audit contracts and how they secure developer workflows. Security teams need to inspect not only contract logic but also unusual data patterns, obscure storage fields and unexplained calls to public RPC endpoints. Developer onboarding and hiring processes need more protection since many of these attacks start with social engineering that tricks engineers into running poisoned code samples.
If the blockchain world adapts quickly, it can turn its own openness and transparency into a strength by making malicious storage easier to detect and harder for attackers to camouflage. But if it does not evolve, on-chain malware could become a long-term problem that undermines trust in Web3 systems and gives state actors a new and powerful tool for covert operation.
Disclaimer: This article is intended solely for informational purposes and should not be considered trading or investment advice. Nothing herein should be construed as financial, legal, or tax advice. Trading or investing in cryptocurrencies carries a considerable risk of financial loss. Always conduct due diligence.
If you want to read more market analyses like this one, visit DeFi Planet and follow us on Twitter, LinkedIn, Facebook, Instagram, and CoinMarketCap Community.
Take control of your crypto portfolio with MARKETS PRO, DeFi Planet’s suite of analytics tools.”