A recent security breach has raised serious concerns about mobile security and has made many people question the idea that iPhones are completely safe for storing digital assets.
Google’s Threat Intelligence Group (GTIG), with Lookout and iVerify, exposed “DarkSword,” a sophisticated iOS exploit kit silently compromising devices since late 2025. For cryptocurrency investors using mobile wallets, this is more than a glitch; it threatens their financial sovereignty.
This article examines the mechanics of the DarkSword exploit, its specific targeting of cryptocurrency data, and the new dimension it represents in the cyber-threat landscape. As we move further into 2026, the central question for the crypto community remains: are mobile devices still a safe control plane for your financial identity, or has the era of the secure smartphone come to an end?
Google Threat Intelligence has exposed “DarkSword”, a full-chain iOS exploit using 6 vulnerabilities to silently compromise iPhones.
Your seed phrases and wallet credentials are a target.
🧵 Here’s what you need to know 👇
— CertiK Alert (@CertiKAlert) March 20, 2026
What You Should Know About the DarkSword Exploit Kit
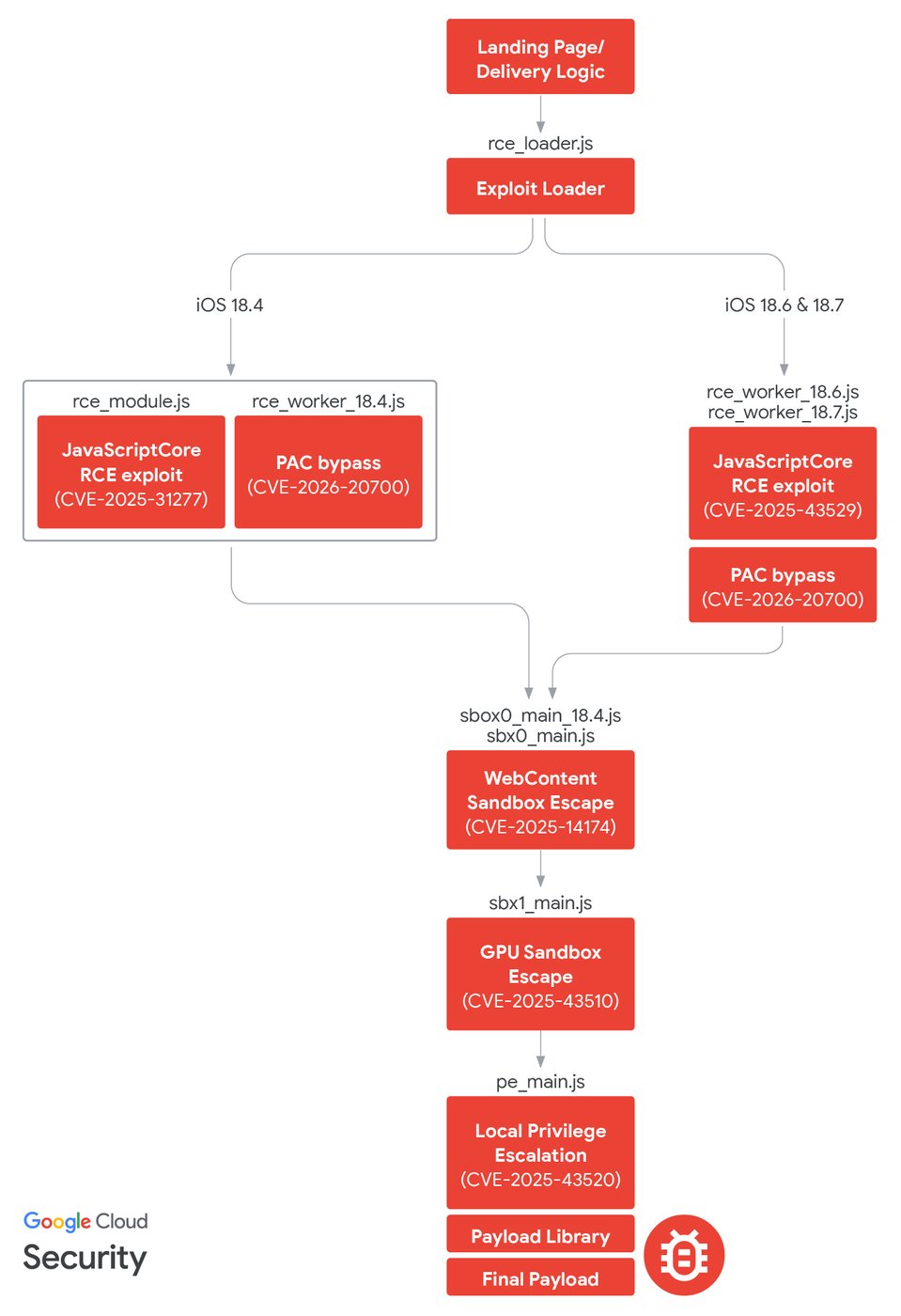
DarkSword is a dangerous exploit that targets iPhones running iOS 18.4 to 18.7. It uses six flaws, including three new zero-day vulnerabilities (like CVE-2026-20700), to silently hack devices when users visit infected websites.
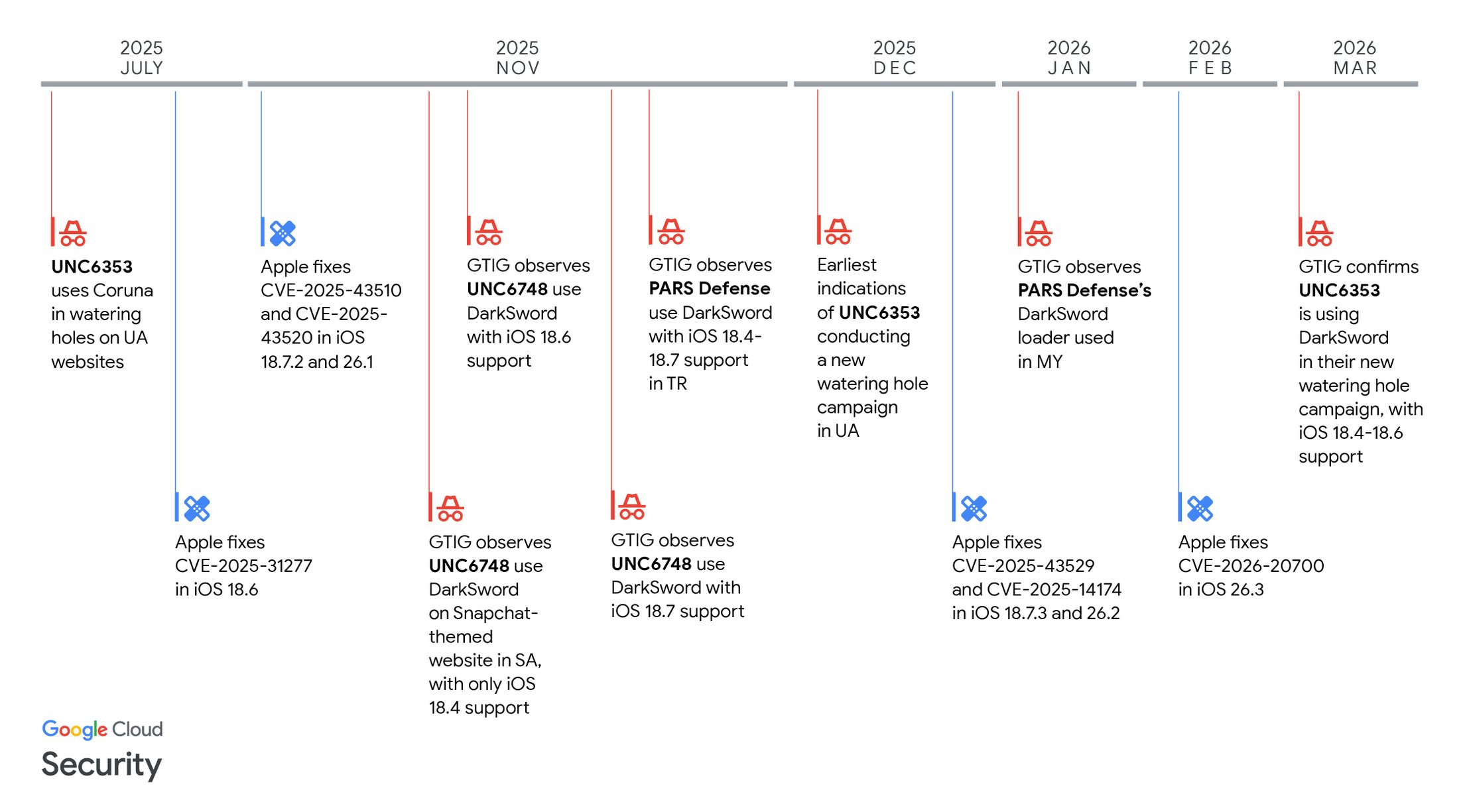
Once in, it quickly steals data, like messages, location, and crypto wallet details, and then cleans up after itself. This exploit was leaked online in March 2026 and is being used by criminals and state-sponsored groups, especially targeting areas like Saudi Arabia and Ukraine.
The Anatomy of a Silent Breach
The DarkSword exploit chain is a masterpiece of malicious engineering, designed to bypass the very “Walled Garden” Apple has spent decades cultivating. Unlike traditional phishing attacks that require a user to download a suspicious file or click a prompt, DarkSword utilizes “watering hole” attacks.
Attackers inject malicious code into legitimate, high-traffic websites such as government portals or news outlets, which then automatically infects vulnerable devices upon visit. The technical depth of the exploit is formidable, leveraging a six-flaw chain across Safari’s WebKit, the iOS kernel, and the Dynamic Link Editor.
Almost the entire attack is written in JavaScript. This allows it to bypass modern iOS mitigations like the Page Protection Layer (PPL) and Secure Page Table Monitor (SPTM). DarkSword is also “fileless”. It hijacks legitimate system processes, rather than installing a visible app. This makes it nearly invisible to traditional detection methods that scan for suspicious files. Once inside, the kit deploys payloads known as GHOSTBLADE, GHOSTKNIFE, or GHOSTSABER. These modules work with surgical speed, often exfiltrating data and self-destructing within minutes to leave no forensic trace.
Expert Perspectives: The Democratization of High-End Spyware
Security experts view the emergence of DarkSword as pivotal in mobile risk assessment. Historically, “zero-click” exploits were the exclusive domain of elite state-sponsored groups. However, DarkSword shows signs of a thriving “second-hand market” for high-end hacking tools.
The shift to financial motivation
Justin Albrecht, Global Director at Lookout, stated that DarkSword represents a structural shift where advanced malware is no longer just for espionage but is actively used for financial gain. This transition suggests that the high ROI of cryptocurrency theft is now attracting the same level of sophistication previously reserved for geopolitical intelligence gathering.
Lowering the barrier to entry
Rocky Cole, Co-founder of iVerify, noted that the evidence proves low-level criminals and non-sophisticated actors now have access to tools that mirror the capabilities of top-tier intelligence agencies.
This democratization is partly fueled by AI-assisted development. Researchers found evidence suggesting that Large Language Models (LLMs) may have been used to assist in developing or customizing the DarkSword code, further lowering the barrier for attackers to maintain complex exploit chains.
A global web of actors
The kit has been linked to diverse actors, including a suspected Russian group (UNC6353), a Turkish commercial vendor (PARS Defense), and another cluster targeting users in Saudi Arabia and Malaysia. This geographic spread indicates that the exploit is being commoditized and sold as a service to various entities with different motives.
Data-Driven Analysis: The Crypto Vulnerability
For the crypto community, the most alarming feature of DarkSword is its explicit focus on financial exfiltration. While earlier kits like “Coruna” focused primarily on messaging and location data, DarkSword includes specific modules to enumerate and steal data from cryptocurrency wallet apps.
The malware specifically targets popular exchange and wallet apps, including Binance, Coinbase, and Ledger Live. By stealing keychain items and browser cookies, attackers can bypass two-factor authentication (2FA) if it relies on SMS or on-device prompts, granting them full access to a victim’s funds. The “hit-and-run” nature of the attack means that by the time a user notices their balance has vanished, the malware has already deleted itself from the device, leaving the victim with no evidence of how the compromise occurred.
Shattering the Walled Garden Myth
The primary implication of DarkSword is the shattering of the “invincible iPhone” myth. Apple’s walled garden was built on the assumption that users are safe as long as they stay within the official App Store. DarkSword bypasses this security model entirely by attacking the gateway to the internet: the browser.
The rationale behind the exploit’s success often comes down to human inertia. Although Apple has patched these vulnerabilities in recent updates, such as iOS 18.7.6 and iOS 26.3.1, hundreds of millions of users delay updates due to a dislike of interface changes or general negligence. This creates a massive attack surface of unpatched devices that remain low-hanging fruit for sophisticated kits.
However, a potential fault in the “just update” argument is that zero-day vulnerabilities, by definition, exist before a patch is available. Even a fully updated phone is theoretically vulnerable to the next iteration of DarkSword. This suggests that for high-value crypto holders, software updates are a necessary, but perhaps insufficient, layer of defence.
From Zero-Click to Developer Exploits: The Democratization of Crypto Theft
The threat landscape is clearly evolving across all fronts, moving far beyond the sophisticated zero-click DarkSword attacks to encompass developer-focused campaigns like OpenClaw, which exploits GitHub, and the integration of crypto exploitation into traditional, organized loan scam rings in Hong Kong. This proves that the barrier to entry for digital asset theft has lowered considerably, demanding that both high-value holders and everyday users abandon reliance on passive security models like the iPhone’s “walled garden.” As long as the ROI of cryptocurrency theft remains high, the community must universally adopt proactive defence strategies, from hardware isolation to critical software updates, to secure their financial sovereignty against this rapidly democratized criminal sophistication.
Securing the Digital Frontier
The DarkSword discovery marks a new era where mobile risk is synonymous with financial risk. The convergence of state-grade technology, AI-assisted coding, and financial motivation has turned every iPhone into a high-stakes target.
To protect your assets, immediate and proactive measures are required:
- Update immediately: Ensure your device is running the latest iOS version (minimum iOS 26.3.1 or 18.7.6) to close the specific holes used by DarkSword.
- Enable Lockdown Mode: If you are a high-value target or hold significant crypto on-device, enable Lockdown Mode in Safari. This blocks complex web technologies that are exploited to gain a foothold.
- Physical Isolation: Move significant assets to hardware wallets. Avoid using a primary smartphone as a “hot wallet” for your entire portfolio.
As attackers move toward more scalable, “zero-click” methods, we must ask ourselves: Will the convenience of mobile banking eventually be outweighed by the inherent risks of an always-connected device?
DarkSword vs. Other Crypto Hacks
Unlike phishing (fake emails) or malware apps needing installs, DarkSword is zero-click via Safari, more sophisticated than Coruna (older iOS target), but similar in crypto focus. It beats SIM swaps (carrier hacks) by being remote and traceless, rivalling Pegasus spyware but cheaper for criminals via exploit markets.
Impact of a DarkSword Hit
A breach steals wallet seeds, private keys, exchange logins, and transaction history in under 60 seconds, enabling instant drains, one campaign hitting up to $270M worth of crypto. You’d see nothing at first: normal battery use, no pop-ups, then empty wallets days later as hackers launder funds.
Can I Consider My iPhone Safe Without Updates?
Simply visiting a compromised website can infect unpatched iPhones with the DarkSword Exploit Kit, even without clicking anything. While Apple fixed these issues in later iOS 26 updates, many iPhones still use vulnerable versions like iOS 18. This exposure allows attackers (linked to Russia and China) to steal sensitive data, including cryptocurrency keys. Ignoring Apple’s update warnings makes regular web browsing risky.
How to Protect Your Crypto
For crypto safety, use cold wallets for most funds and only keep small amounts for trading on exchanges. Always use app-based 2FA and strong, unique passwords (12-16 characters with mixed types) for all accounts. Update your iPhone’s iOS right away to patch vulnerabilities like DarkSword. Avoid suspicious websites and check your wallet often for unusual activity. Use a password manager and reduce your reliance on exchanges for better security against mobile theft.
Disclaimer: This article is intended solely for informational purposes and should not be considered trading or investment advice. Nothing herein should be construed as financial, legal, or tax advice. Trading or investing in cryptocurrencies carries a considerable risk of financial loss. Always conduct due diligence.
Enjoyed this piece? Bookmark DeFi Planet, explore related topics, and follow us on Twitter, LinkedIn, Facebook, Instagram, Threads, and CoinMarketCap Community for seamless access to high-quality industry insights.
“Take control of your crypto portfolio with DEFI PLANET PRO, DeFi Planet’s suite of analytics tools.”